## Third task - Postern Now it's time for the 3rd task, and this one was much more challenging than the previous one. From the previous task, we learned that the data for this challenge is located at memory address 0x30000, and just like in both previous tasks we also get an error message...
>/Posts/[1:6]/20 $
2026
## The Second Task Continuing the series, let's check what's inside the second task. 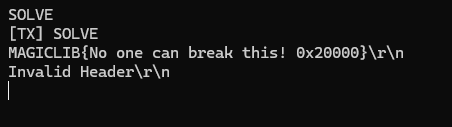 So now we can search for "**Invalid Header**". And there is exactly one hit! This message is shown when the condition involving the *parapet* function fails. ...
26 Feb
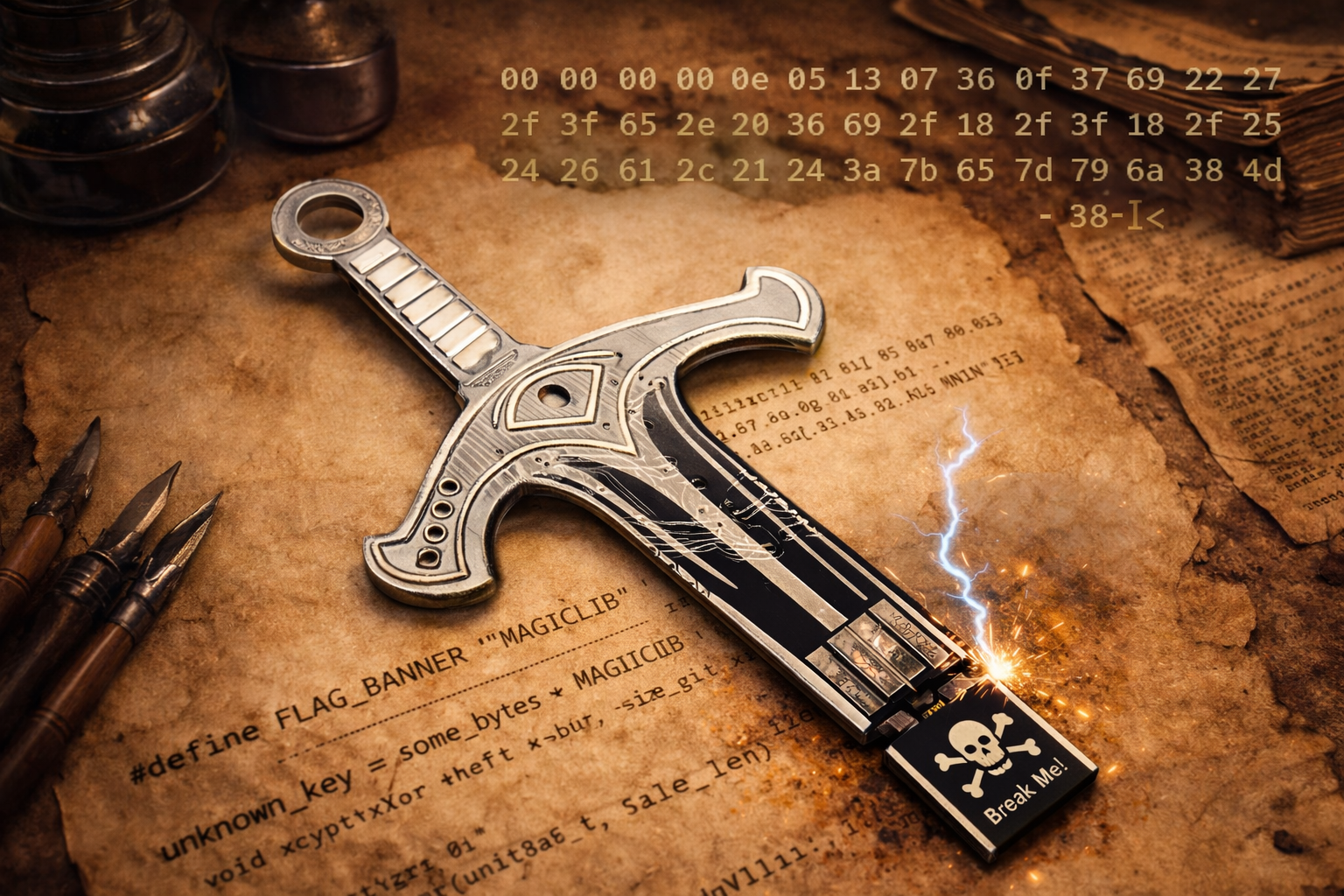
## What is even this task about? Ok, so last time we ended up with some bunch of weird looking bytes; > 00 00 00 00 0e 05 13 07 36 0f 37 69 22 27 3f 65 2e 20 36 69 2f 3b 3f 24 26 61 2c 21 24 3a 7b 65 7d 39 6a 79 7d 79 6a 38 4d 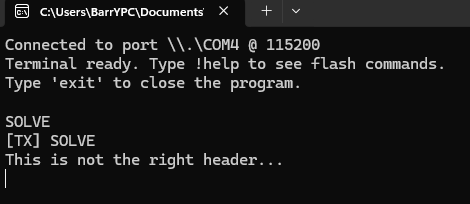 Attempt to **SOLVE**...
20 Feb
## What's that? Because I need to practice my skills in IoT and physical security of electronic devices, I decided to buy the Sword of Secrets hardware crypto CTF kit, which recently arrived. If you don't know what that is, don't worry you haven't missed anything important. In this post I'll...
19 Feb
## Introduction Quite a few of my posts focus on solving challenges involving reverse engineering of mobile applications from CTF competitions. Although in one of my previous posts I briefly described how to approach this topic, I'd like to cover it more extensively here, highlighting...
3 Feb
2025
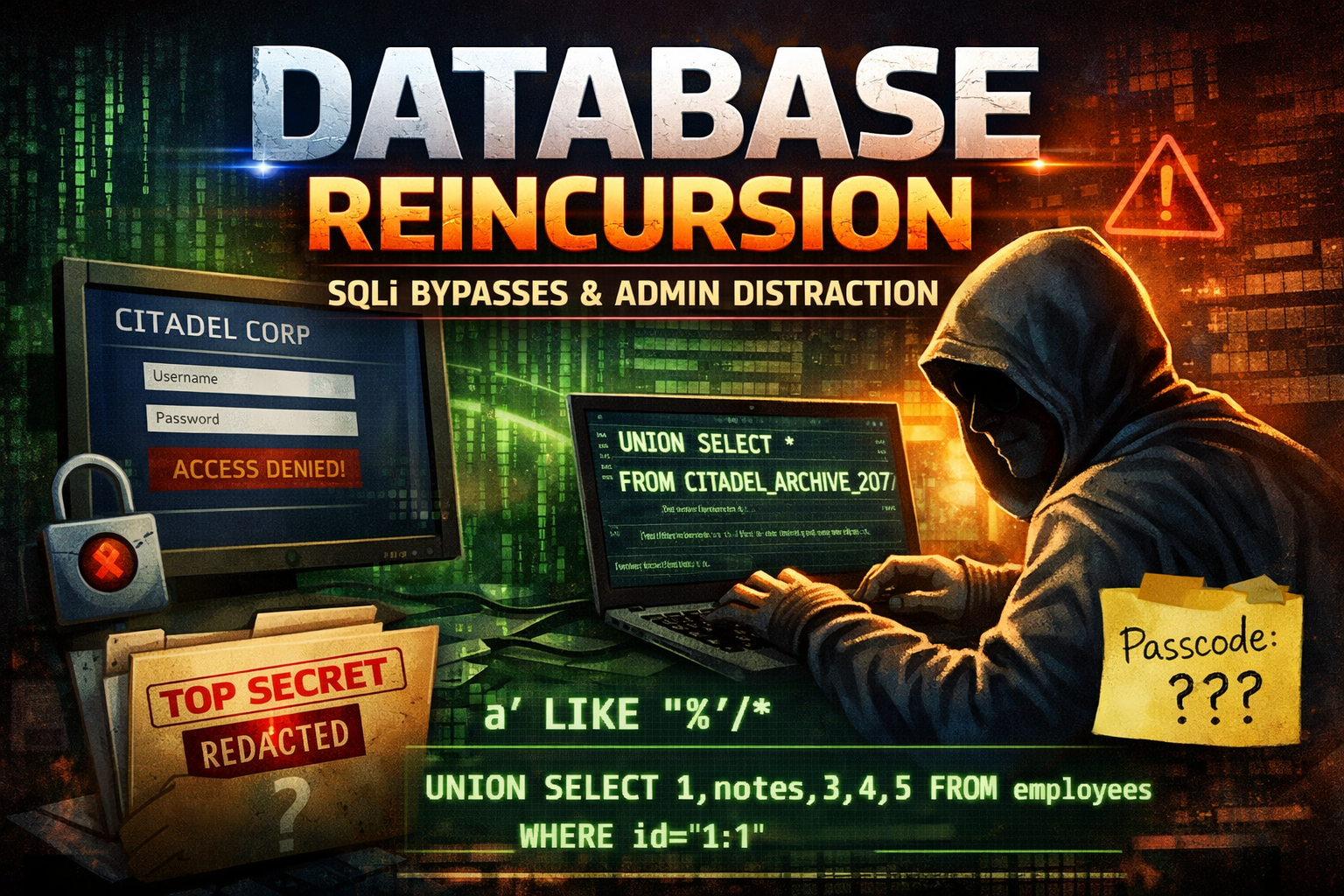
# First Part ## Recon To be honest we don't have much to see there. It's simple login form shown on the screenshot below:  And we don't have any credentials attached to this task so I assumed it's a SQLi kind of a task and tried some basic payloads as input.